For those curious about the inner workings of their network, Wireshark is an invaluable tool. Often referred to as the "Swiss Army Knife" of network protocol analyzers, it empowers you to see what's happening on your network at a microscopic level. But what exactly is it, and what can it do? ...
Dissecting the Digital: What is Wireshark?
At its core, Wireshark is a free and open-source network protocol analyzer. Imagine it as a powerful magnifying glass, allowing you to capture and inspect individual packets of data flowing through your network. Each packet carries information, and by dissecting them, Wireshark reveals the protocols used, source and destination addresses, and even the actual data content (depending on the protocol).
Feature Frenzy: What Can Wireshark Do?
Wireshark boasts a staggering array of features, making it a versatile tool for various tasks:
Live and Offline Analysis:
Capture packets in real-time or analyze previously captured data files.
Deep Protocol Inspection:
Decode and analyze hundreds of protocols, including common ones like TCP/IP, HTTP, DNS, and even VoIP. New protocols are constantly added.
Multi-Platform Compatibility:
Runs seamlessly on Windows, Linux, macOS, and other platforms.
Powerful Capture and Filter Options:
Capture data from specific interfaces, filter captured packets based on various criteria (e.g., source address, protocol), and even color-code them for clarity.
Detailed Packet View:
Each packet is dissected into its header and payload, with detailed information displayed about each layer.
Conversations and Stream Follow:
Reconstruct complete conversations between devices and follow data streams across multiple packets.
Expert Tools and Plugins:
Extend functionalities with a wide range of dissectors, decryption tools, and custom plugins.
Statistics and Graphs:
Gain insights into network traffic patterns with various statistics and graphical representations.
Applications of Wireshark:
With its diverse capabilities, Wireshark caters to various needs:
Network Troubleshooting:
Identify and diagnose network issues like slow connections, dropped packets, or routing problems.
Security Analysis:
Detect suspicious activity, analyze malware communication, and investigate security breaches.
Performance Monitoring:
Monitor network traffic volume, identify bottlenecks, and optimize network performance.
Protocol Development and Testing:
Understand protocol behavior, debug network applications, and test network devices.
Education and Research:
Gain insights into network protocols, learn about network operations, and conduct research in various fields.
Beyond the Basics:
While powerful, Wireshark has a learning curve. Understanding network protocols and basic networking concepts is crucial to extract meaningful information. Additionally, responsible and ethical use of Wireshark is essential, respecting privacy and adhering to network policies.
Wireshark is an essential tool for anyone curious about the hidden world of network traffic. Its versatility, open-source nature, and active community make it an invaluable resource for network professionals, security analysts, developers, and even inquisitive learners. So, if you're ready to peek under the hood of your network, give Wireshark a try and see what it can reveal!
Wireshark - Changelog.
How to use Wireshark:
Wireshark is a popular network protocol analyzer that allows you to inspect the data traveling back and forth on a computer network.
Here's a basic guide on how to use Wireshark:
1. Download and Install Wireshark:
- Download the latest version for your operating system.
- Follow the installation instructions for your platform.
2. Launch Wireshark:
- Open Wireshark after installation. On Windows, you can find it in the Start menu or desktop. On Linux, you can usually launch it from the application menu or a terminal.
3. Select Network Interface:
- Upon opening Wireshark, it will ask you to choose a network interface. Select the interface that corresponds to the network you want to monitor (e.g., Wi-Fi or Ethernet).
4. Start Capturing Packets:
- Click on the interface you want to capture packets from, then click the "Start" button (usually a shark fin icon) to begin capturing packets.
5. Capture Filters (Optional):
- You can use capture filters to limit the types of packets captured. For example, you can filter by IP address, port, or protocol. Click on "Capture" > "Capture Filters" to set filters.
6. Stop Capturing:
- Once you've captured enough data, click the "Stop" button (usually a red square) to stop the packet capture.
7. Analyze Captured Packets:
- The main Wireshark window displays a list of captured packets. You can click on any packet to view its details in the lower pane.
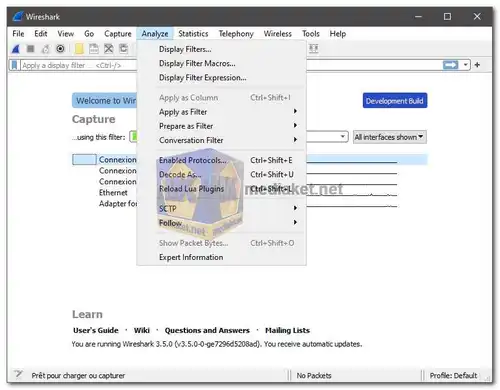
- You can use various filters and tools to analyze the captured data. For example, you can filter by protocol, source or destination address, and more.
8. Follow TCP Stream:
- Right-click on a packet and select "Follow" > "TCP Stream" to see the entire conversation between two hosts in a more readable format.
9. Exporting Data:
- You can export captured packets for further analysis or sharing. Go to "File" > "Export Packet Dissections" to save the data in various formats.
10. Profile Your Captures:
- Wireshark provides various statistics and graphs under the "Statistics" menu, which can help you analyze network behavior.
11. Apply Display Filters:
- Use display filters to focus on specific types of traffic. Enter a filter in the display filter bar (e.g., `http` to show only HTTP traffic).
12. Learn and Explore:
- Wireshark has a lot of features and capabilities. Explore its menus and settings to discover more advanced functionalities.
Keep in mind that capturing packets on a network may have legal and ethical implications. Make sure you have the right permissions and comply with applicable laws and policies before using Wireshark on a network.
Download Wireshark:
Wireshark v4.2.6 - For windows 64 bit:
Install version - Size: 82.48 MB - Download
Portable version - Size: 51.16 MB - Download
Wireshark v3.6.19 - For windows 32 bit:
Install version - Size: 58.50 MB - Download
Portable version - Size: 38.01 MB - Download